Amazon recently unveiled REX (Trusted Remote Execution), a secure script execution engine that allows only authorized operations for each specific script. This means that if a script is designed to parse logs, it will solely be able to read the logs and any unauthorized attempts to alter or delete files will be prevented. The REX code is written in Rust and is open source under the Apache 2.0 license. For more details, visit the official GitHub repository.
REX can be utilized to oversee and restrict the actions carried out by scripts generated by AI agents when handling system automation requests. By utilizing REX, the owner of the host can prohibit inappropriate actions and manage which operations are permitted, regardless of the requests issued to the AI agent. This proactive approach helps in thwarting potential attacks where threat actors exploit query substitution to AI agents to execute unauthorized actions within the system.
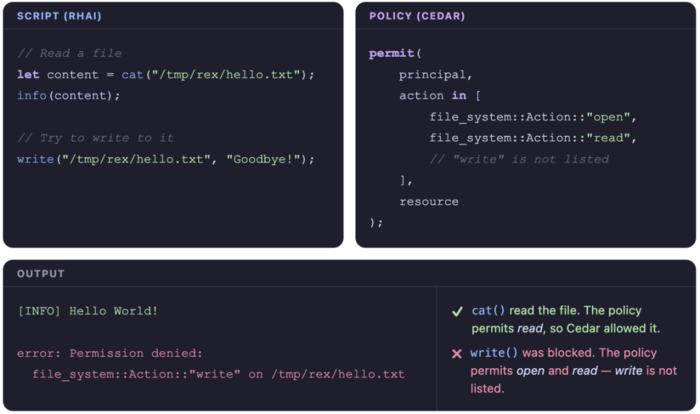
Scripts in REX are written using the Rhai language, which employs dynamic typing and combines syntax elements of JavaScript and Rust. Cedar rules attached to the script govern each system operation executed by the script. The scripts run in an isolated sandbox environment where only specified file operations, networking capabilities, process controls, and other system functionalities are allowed.
Furthermore, every system call, like opening, reading, or writing a file, undergoes authorization based on the designated rules before being executed. The security model operates on the premise that rules are distinct from scripts and are defined by the service owner rather than the script creators or users. To prevent race conditions in scripts and symlink attacks, scripts prefer using file descriptors over paths whenever feasible.
By default, scripts executed by the REX engine do not have direct access to the host and conduct operations through authorized Rust APIs. For a visual representation, you can check out the diagram below: