In the unofficial Telegram client Nekogram, hidden obfuscated code was discovered sending phone numbers of users to the bot “@nekonotificationbot”, linked to user ID. The change for collecting phone numbers was found only in APK packages distributed through Google Play, GitHub, and the project’s Telegram channel. The source code on GitHub and in the APK package from the F Droid directory did not contain the code collecting phone numbers.
The backdoor was detected in the Extra.java file, with reports suggesting that the sending began with Nekogram version 11.2.3, starting initially with users with Chinese numbers and later expanding to all users. The program also utilized osint bots “@tgdb_search_bot” and “@usinfobot” to identify users by their ID, although no phone numbers were sent to these bots.
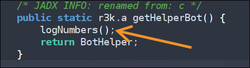
Researchers developed a java-hook and bot to allow users to verify if their application instance was sending phone numbers. The tool can be accessed here.
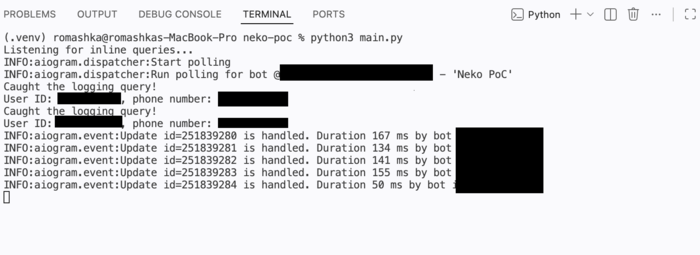
According to the researchers, the program’s authors could potentially use the collected information to create a database for sale to OSINT bot creators. The deliberate concealment of this activity is evident through obfuscated changes and the use of inline queries to send data. Following the disclosure of the issue in the project’s bug tracking system, the author of Nekogram acknowledged the sending of phone numbers to the bot, although the reason for this activity was not explained. The author mentioned that the sent phone numbers were not stored or shared with anyone.
In addition, a vulnerability was identified in the official Telegram application by