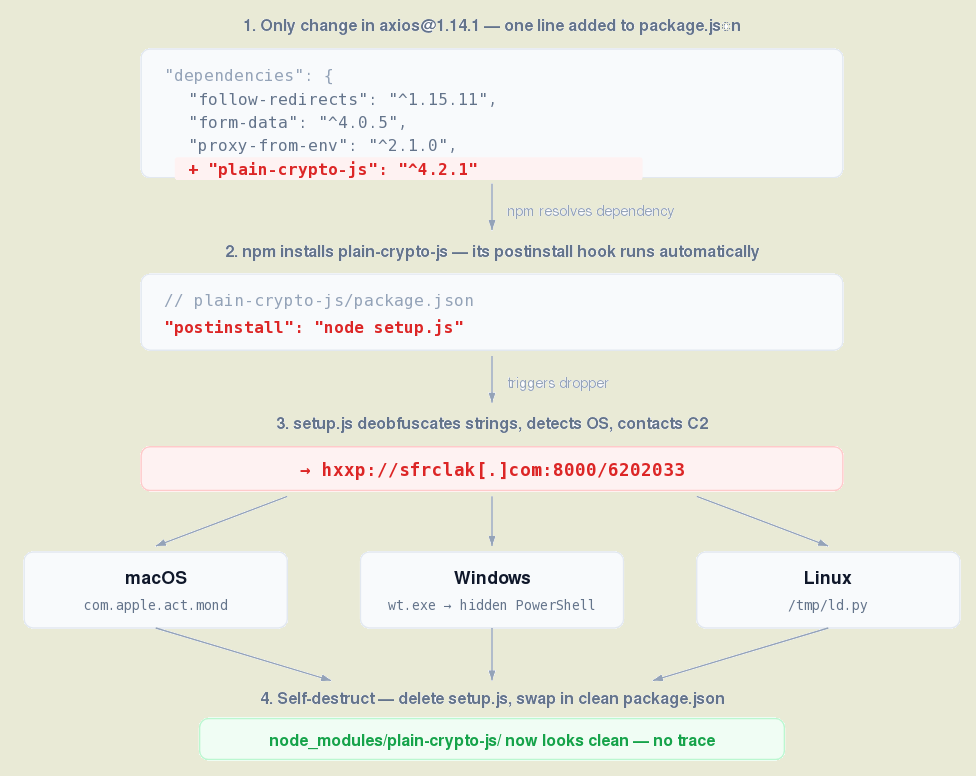
In a recent security incident, attackers were able to compromise the maintainer’s account of the NPM package axios, which is a popular HTTP client implementation for browsers and Node.js with over 100 million downloads per week. The attackers released two malicious versions of the axios package (1.14.1 and 0.30.4) by injecting a bogus dependency plain-crypto-js 4.2.1 containing code that communicated with the attackers’ command and control server. These malicious versions were available for download on March 31 for nearly 3 hours.
The attackers bypassed the standard release mechanism and posted the malicious versions directly on NPM using the maintainer’s credentials. It is believed that they obtained the NPM access token of the maintainer (“jasonsaayman“) to carry out this attack. The specific method of how the access token was stolen remains unclear.
The malicious code, hidden in the plain-crypto-js package, was triggered after the axios package was installed and executed a postinstall handler that downloaded and installed a Trojan on systems running Windows, macOS, and Linux. To avoid detection, the malicious component deleted certain files after execution.
On macOS, the malicious executable was disguised as “/Library/Caches/com.apple.act.mond”, on Windows as “%PROGRAMDATA%wt.exe”, and on Linux as “/tmp/ld.py”. Once activated, the Trojan communicated with the attackers’ server every 60 seconds, allowing them to execute commands on the compromised system and steal sensitive information.
The malicious activity on Linux and macOS was designed for quick data collection without persistence after reboot, while on Windows a file “%PROGRAMDATA%system.bat” was created to retrieve the malicious component each time the system was restarted, enabling the attackers to maintain access to the compromised system.