Researchers from the University of California, Riverside developed (PDF) a new class of attacks on wireless networks – AirSnitch. The attacks make it possible to bypass client isolation mechanisms in a Wi-Fi network, which prevent clients from directly accessing each other. In the worst case scenario, attacks allow
the attacker can redirect the victim’s traffic (MITM) through himself to analyze or modify unencrypted requests, as well as spoof requests to sites through DNS cache poisoning.
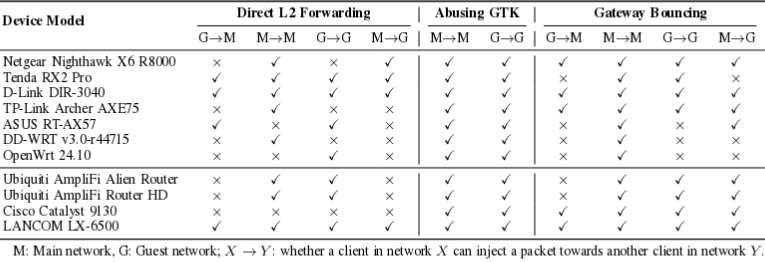
To carry out attacks, the attacker must be able to connect to the same wireless network as the victim, or to a guest network served by the same access point. For example, attacks can be used on public public wireless networks. Of the 9 tested models of wireless access points from Netgear, Tenda, D-LINK, TP-LINK, ASUS, Ubiquiti, LANCOM and Cisco, as well as solutions with DD-WRT and OpenWrt firmware, all of the devices were susceptible to at least one attack method.
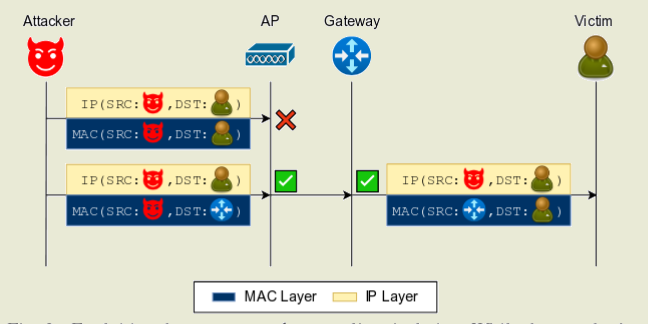
There are three problems that make it possible to carry out an attack. The first problem bypasses isolation between clients due to incorrect key management used to protect broadcast frames. The second problem is that isolation is usually applied at the MAC level or at the IP level, but not at both levels at the same time. The third problem is caused by unreliable synchronization of client IDs at the level of the entire network stack, which allows intercepting incoming and outgoing traffic from other clients.
Modern wireless access points combine the functions of a radio transmitter and a network switch (Layer 2 Switch), while the switch, unlike wired networks, instead of binding the client to a physical port, uses a logical binding to the wireless channel. The client’s MAC address is used as an identifier for this binding, which is identified with the channel in a special MAC address table. If the client switches to another channel (for example, after moving from 2.4 GHz to 5 GHz), the data in the table is updated.
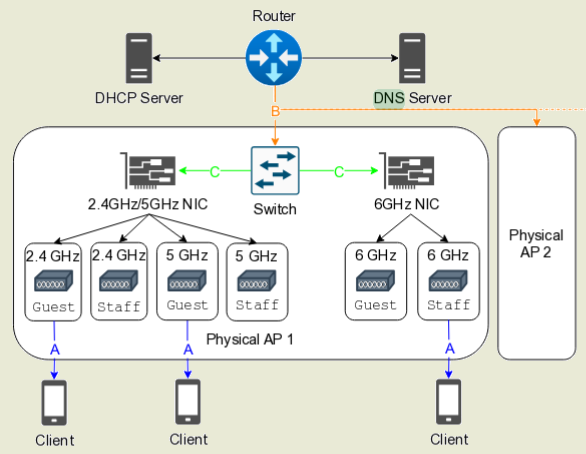
The attack is carried out on the first (physical, radio channel) and the second (channel, MAC address) levels of the OSI network model, and boils down to the fact that an attacker who has connected to the same access point, but using a frequency range different from the victim’s (for example, 2.4 GHz instead of 5 GHz), sends a request to negotiate the connection (4-way handshake), indicating the victim’s MAC address (similar to ARP spoofing in Ethernet networks). Since clients are identified by MAC address, the access point assumes that the client has switched to another channel and changes the entry in the MAC address table. After this, incoming traffic from the access point begins to be sent to the attacker’s device.